E mal injection? Don’t panic. In today’s digital landscape, cybersecurity is paramount. Hackers constantly devise new ways to breach systems, and e mal injection is a common tactic. By embedding malicious code into email messages or web forms, cybercriminals aim to exploit vulnerabilities. Understanding how to spot and prevent e mal injections is crucial for safeguarding your online presence. Let’s delve into the world of e mal injections and empower you to protect yourself in the virtual realm.
The Perils and Precautions of Email Injection: Safeguarding Your Inbox
Introduction
In this digital age, email has become an indispensable part of our lives. Whether it’s communicating with friends, family, or colleagues, or receiving important updates and notifications, our inboxes are constantly buzzing with activity. However, amidst the convenience and efficiency that email provides, there lurks a hidden danger – email injection.
What is Email Injection?
Email injection is a malicious technique used by cybercriminals to manipulate email servers and inject harmful code or content into emails. These injected emails often appear legitimate, making it challenging for users to detect them. Once opened, these emails can unleash a host of threats, including malware, phishing attempts, and even identity theft.
Types of Email Injection
There are several common types of email injection techniques used by hackers:
1. **HTML Injection**: In this type of attack, hackers inject malicious HTML code into emails to exploit vulnerabilities in email clients or web browsers.
2. **SQL Injection**: Hackers use SQL injection to manipulate databases and extract sensitive information from email servers.
3. **Cross-Site Scripting (XSS)**: XSS attacks involve injecting malicious scripts into emails to steal login credentials or personal data.
4. **Attachment Injection**: Hackers may attach malicious files or links to emails, which, when opened, can infect the recipient’s device with malware.
Signs of Email Injection
Detecting email injection can be tricky, as the emails often appear convincing at first glance. However, there are some telltale signs that can help you identify a potentially malicious email:
1. **Unsolicited Attachments**: Be wary of emails that contain unexpected attachments or links, especially from unknown senders.
2. **Urgent Requests**: Emails that pressure you to take immediate action or provide sensitive information should be treated with caution.
3. **Spoofed Senders**: Check the email address carefully to ensure it matches the legitimate sender’s address.
Impact of Email Injection
The consequences of falling victim to email injection can be severe. From financial loss and data breaches to compromised personal information, the fallout can be catastrophic. Moreover, email injection attacks can tarnish your reputation, both personally and professionally, leading to distrust among recipients.
Protecting Yourself from Email Injection
Safeguarding your inbox from email injection requires a proactive approach and adherence to best practices. Here are some essential tips to fortify your defenses:
1. **Use Strong Passwords**: Ensure your email account is protected by a robust, unique password that includes a mix of letters, numbers, and special characters.
2. **Enable Two-Factor Authentication**: Adding an extra layer of security through two-factor authentication can thwart unauthorized access to your email account.
3. **Stay Updated**: Keep your email client and antivirus software up to date to shield against potential vulnerabilities and exploits.
4. **Be Skeptical**: Exercise caution when opening emails from unknown sources or clicking on suspicious links. When in doubt, verify the sender’s identity before taking any action.
Conclusion
In conclusion, email injection poses a significant threat to your online security and privacy. By understanding the risks, recognizing the signs, and adopting proactive security measures, you can safeguard your inbox against malicious attacks. Remember, staying vigilant and informed is key to protecting yourself in the ever-evolving landscape of cybersecurity. Stay safe, stay secure, and keep those emails free from injection risks!
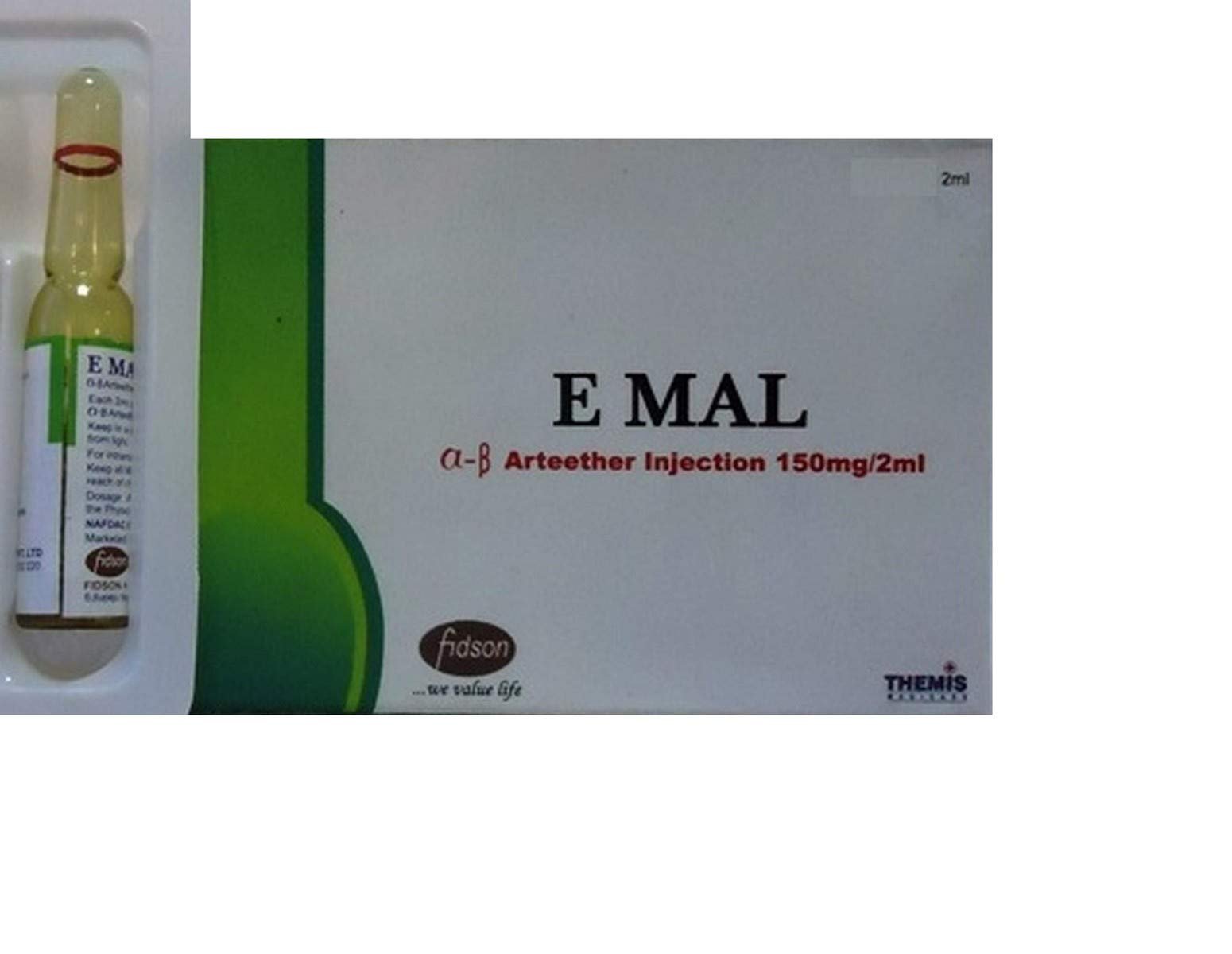
Alpha Beta arteether injection | Match injection | Emal injection | E mal injection
Frequently Asked Questions
What is e-mail injection and how does it occur?
E-mail injection is a type of cyber attack where malicious code or commands are injected into an email message to exploit vulnerabilities in the email system. This can happen when an attacker manipulates the email headers or content to trick the recipient’s email client or server into executing unauthorized actions.
What are the potential risks associated with e-mail injection attacks?
The risks of e-mail injection attacks include unauthorized access to sensitive information, financial losses, malware infections, and reputation damage. Attackers can use e-mail injection to launch phishing attacks, spread malware, or steal confidential data from the targeted organization or individual.
How can organizations protect themselves against e-mail injection attacks?
Organizations can protect themselves against e-mail injection attacks by implementing email security best practices such as using email filtering systems to detect and block suspicious emails, educating employees about phishing awareness, regularly updating email software to patch known vulnerabilities, and implementing strong authentication mechanisms.
Final Thoughts
Hackers continue to exploit vulnerabilities, with e-mail injection remaining a prevalent threat. Protect sensitive information by implementing robust email security measures. Stay vigilant against phishing attempts to prevent e-mail injection attacks. Remember, regular staff training is key to maintaining a secure email environment.